The main list of CVEs for Java can be found at CVE Details. Some have ended up under Oracle instead of Sun.
If you use Java on a server or on a mobile phone, there are different vulnerabilities. JBoss and Oracle Application Server are two of the most popular J2EE setups. Tomcat is by far the most popular Java server product.
Read more »Check out the Development tag for another article on Java.
While most of this site is about exploiting Java, remember that exploiting Java sometimes requires advanced knowledge of Java. Let's take a quick look at a snippet of code.
class j4vaThrow
{
void printJohn()
{
String name = "Peter";
String age = "48";
String description = name + " is " + age + " years old.";
System.out.println("result:" + description);
throw new RuntimeException("It was a bad idea.");
}
// public
public static void main(String [] args)
{
j4vaThrow a = new j4vaThrow();
a.printJohn();
}
}
Runtime Exceptions have a specific use. Unlike normal exceptions, Runtime Exceptions don't need to be caught. Looking the documentation, we can see that NullPointerException is a subclass of RuntimeException. That means that if you set a variable to null and then call a method, you get a NullPointerException and the compiler won't complain about it. Why do we care about this? There's a great article here about Java Anti-Patterns.
Read more »The first applets to discover are the Demo Applets. If you have installed the JDK, they can be found in demo/applets. Note that the JDK 7 distributes the demos in a separate package. Alphabetically, we can start with Animator example 1. If you want to run it natively instead of in a browser for now, use appletviewer:
appletviewer /opt/jdk1.6.0_31/demo/applets/Animator/example1.html
The Animator example html links to source code for Animator.java, which contains classes Animation, AnimationFrame, DescriptionFrame, and ParseException. Using our decompiler, jd-gui we can retrieve the source from the .class file.
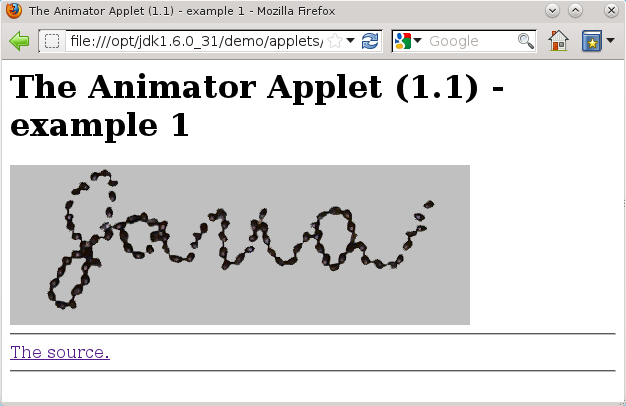
If you have trouble running this on Linux (especially Gentoo), it's possible that you need to mess around with your Java plugins. For me, this did it:
ln -s /opt/jdk1.6.0_31/jre/lib/i386/libnpjp2.so ~/.mozilla/plugins/libnpjp2.so
So now let's look into the running of this Applet. First of all, notice that you didn't have to click a "Are you sure?" dialog box for this Applet. The reason for this is the security model allows simple applets to run without confirmation. For detailed information about this see What Applets Can and Cannot Do by Sun/Oracle. It says that this Applet cannot do harm to your local system, so we don't have to ask you about it. What about signed Applets? It says there that signed Applets can do bad things to your system. Chapter 10: Signed Applets from Advanced Programming for the Java 2 Platform explains how we go about signing a potentially malicious Applet. For the impatient:
javac SignedAppletDemo.java jar cvf SignedApplet.jar SignedAppletDemo.class keytool -genkey -alias signFiles -keystore compstore -keypass kpi135 -dname "cn=j4va.com" -storepass ab987c jarsigner -keystore compstore -storepass ab987c -keypass kpi135 -signedjar SSignedApplet.jar SignedApplet.jar signFiles
Then we put the applet into an HTML file like this:
<applet archive="SSignedApplet.jar" code="SignedAppletDemo.class" height="100" width="300"/>It gives us this big warning:
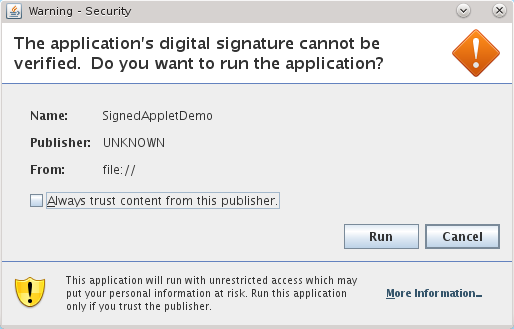
Assuming that we don't have a $200 code-signing key (which I don't yet) this warning looks pretty good, right? For $200, you get a much nicer looking warning. CERT thinks it's dangerous and so should you. There's nothing stopping a malware producer from buying as many code signing certificates as he needs.
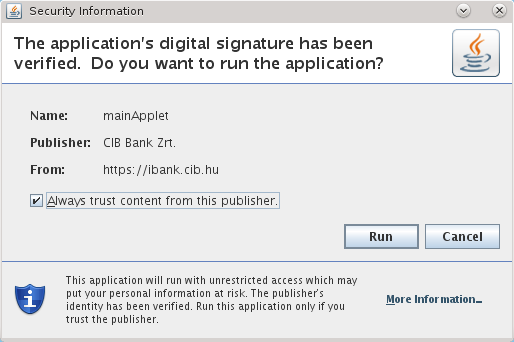
We should also note that the checkbox is checked by default, so one accidental click means Java insecurity for a long time.
Hackers and malware authors have been using this for years. This can't be used lightly though. The attacker must be sure that the victim will click Run. How does the malware author know? The malware author only needs to lure the victim into making the mistake. The promise of free warez, a cell phone unlock key, or photos has fooled many people.
But malware authors don't actually have to resort to this. Since they can find out the version of Java running without asking the user, any user who has an old version of Java can be exploited instead. The past 2 years has seen an unprecedented number of vulnerabilities in Java, most of which have publicly available exploits requiring no expertise.
So now that we've subverted the Applet system to get arbitrary code execution on millions of home user's machines, let's talk about how to disable Java on our own machines.
Disable Java on Firefox
Disable Java on IE
Disable Java in Chrome
Disable Java in Opera
Disable Java icon
Android runs on Java amongst other things.
Android's use of Java is special in several ways. The Android API differs greatly from other standard Java J2SE and J2ME APIs. Secondly, the use of the Dalvik VM means that Android packages cannot just be run under desktop operating systems such as Linux, Windows, or Mac OSX. This may seem counter-intuitive because Android is built on Linux. The difference between the Android OS and the Linux OS is significant and not easily fixed.
Android malware is on the rise. There are two reverse-engineering articles under Malware.
Read more »